Endpoint Protection 7.70

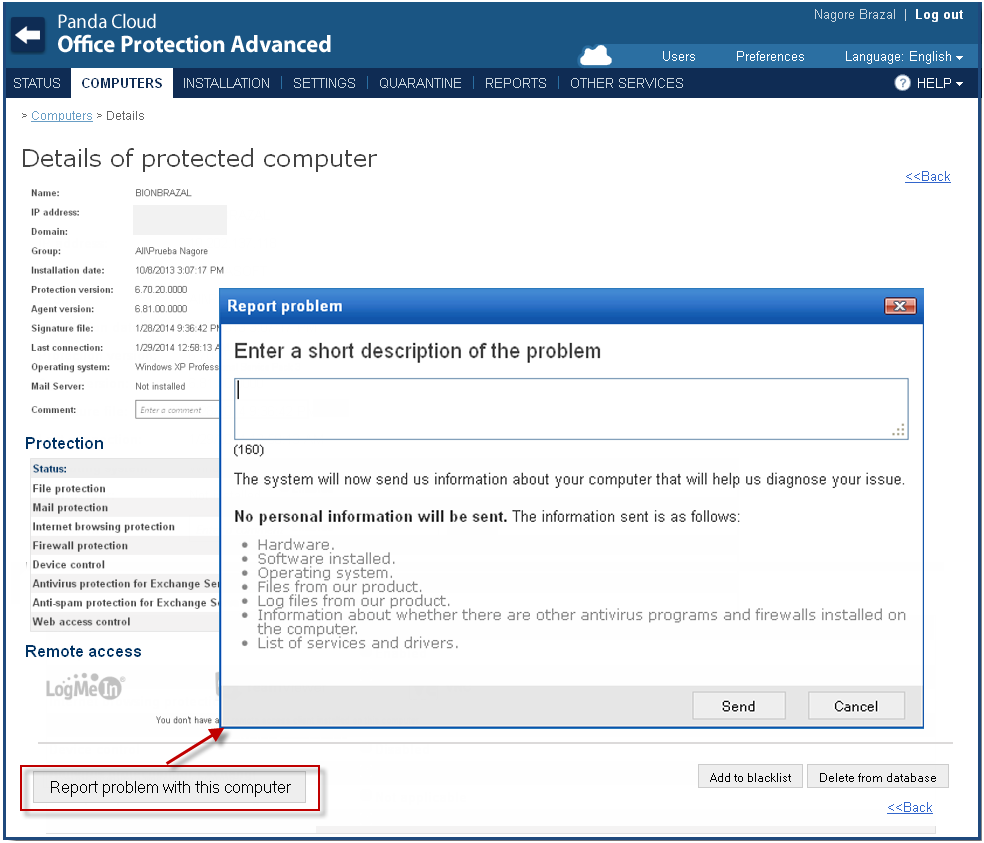
New Panda Remote Control.
From this version onwards, Panda gives you the option to purchase the new module Panda Remote Control integrated within your Endpoint Protection management console.
Troubleshoot security incidents and technical issues remotely without disrupting users.
Panda Remote Control includes the following features:
- Remote desktop access with administrator rights.
- Remote service and process management across your IT network.
- Remote command line.
- Bidirectional file transfer.
All this with the peace of mind of knowing that Panda Remote Control encrypts all communications between your computers at all times.
Compatibility with Server Core servers
Now, Adaptive Defense and Adaptive Defense 360 let you protect and monitor your Server Core servers.
From version 2.4 onward, you can safeguard your Server Core installations of Windows Server 2008, 2008 R2, 2012 and 2012 R2 against malicious infections.
New version of the Mac protection
The new version (10.9.120.00.749) includes a new and improved engine for the protection for OS X systems.
This version is compatible with Mac versions 10.8 (Mountain Lion) and above.